What is ISO/IEC 27001:2022?
ISO/IEC 27001:2022 is the leading international standard for information security management systems (ISMS), jointly published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC).
It sets out the criteria for establishing, implementing, maintaining, and continually improving an ISMS — including requirements for assessing and treating information security risks. The standard applies to organizations of all types and sizes, helping them systematically protect sensitive data, comply with legal requirements, and strengthen business resilience.
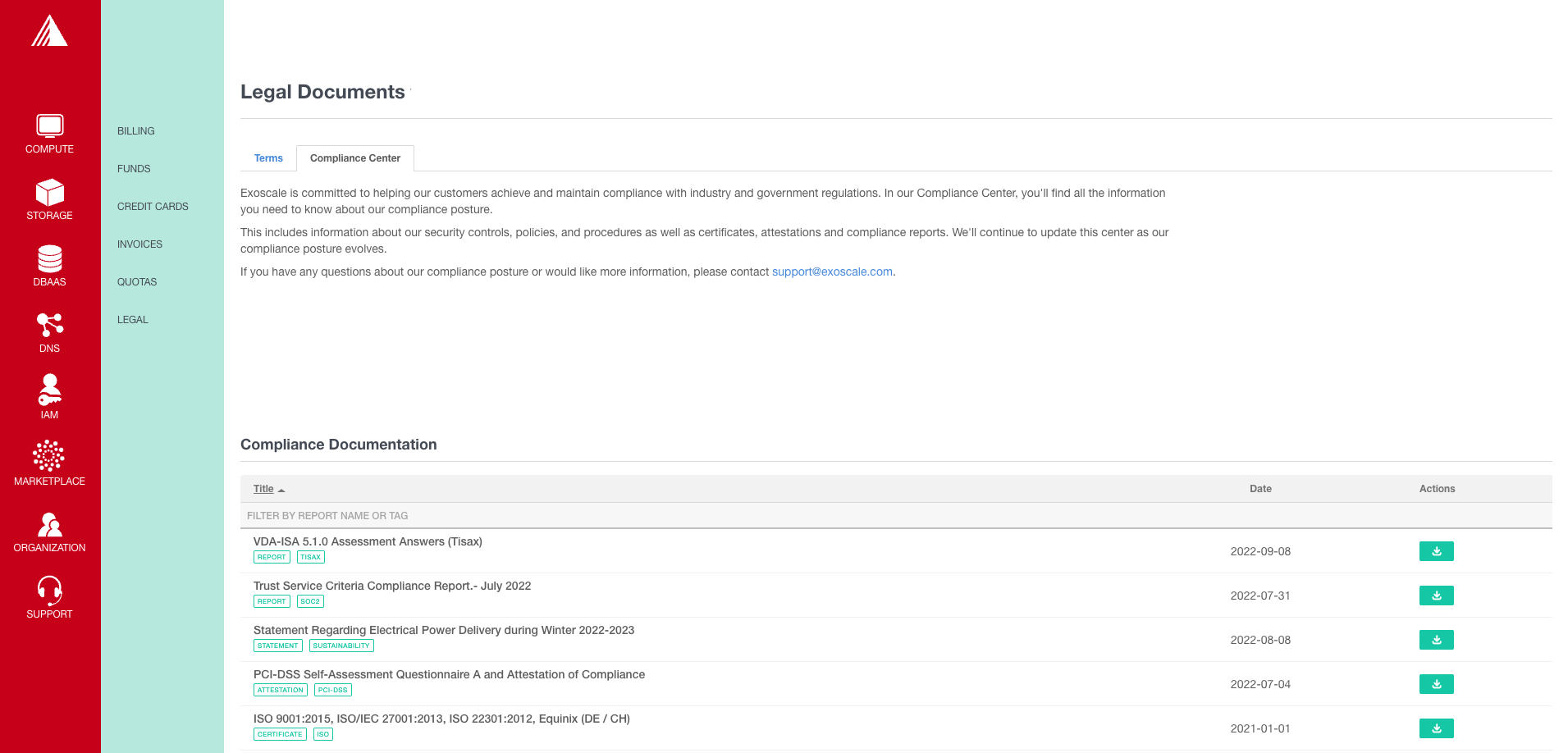
Access the certificate and audit reports via our Compliance Center.